Phishing of Mexican banks
Yesterday we received notice of a series of emails that are spreading malware through a campaign of scam related to the Tsunami in Japan.
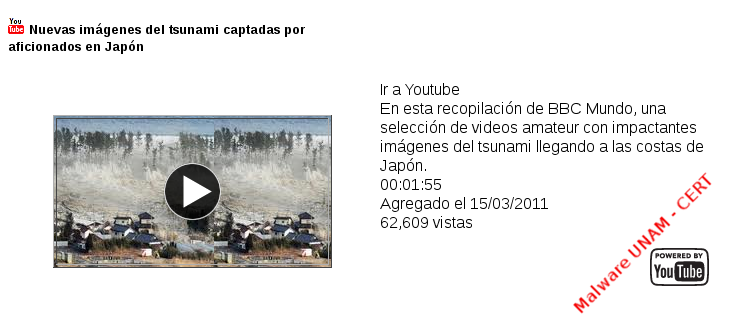
In the mail an alleged Youtube video which make reference to "shocking images" of the unfortunate event that strucks Japan last March 11 is shown. When the user tries to watch it "clicking" on the image, it is redirected to a site from which you can download the executable Install-flash.exe, which refers to the alleged flash plug-in needed to play the video.
When analyzing the sample, with different antivirus engines, the following ones detected it as threat:

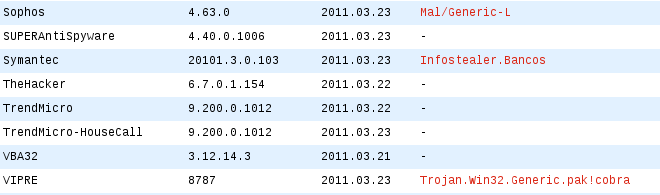
Its hashes are:
When running the sample in our laboratory, a window is displayed with an Error message, apparently because of Kernel32.dll file was corrupt.

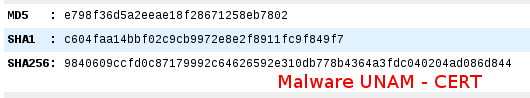
However, the malware manages to carry out the Hosts file modification, setting the Pharming of Bancomer and Santander.

Yesterday, the phishing bank sites were still active:
Bancomer:
http://195.XXX.XXX.38/modules/03/index.html
Santander:
http://195.XXX.XXX.38/modules/mexico/index.htm


Reviewing the pages of banks, we found no differences regard to phishing sites. However, we identified through an inserted frame by compromising the site http://195.XXX.XXX.38, was possible to accomplish the scam.
The real danger of such attacks is that an inexperienced user can be tricked with greater ease, as before, with only verify the domain in the navigation bar, one could realize if something was wrong and get away immediately from the site. But now, with this technique, verify the domain is not enough because we are in the official website, but the confidential information will be sent to the attacker without the user acknowledgement.
To prevent this type of deception, can be useful the installation of extensions (add-ons) to identify the IP address of the site in which we are visiting, in Firefox there is one called ShowIP (https://addons.mozilla.org/en-us/firefox/addon/showip/) that does just this. In addition, it becomes essential to keep our browser updated, as they now have implemented security features that identify these threats.
